Multi-Factor Authentication
Strong passwords are essential, but they aren't enough. Phishing attacks and data breaches put your account at risk. Multi-Factor Authentication (MFA) provides extra security for your FLCC Account. Some services and websites refer to MFA as two-step authentication (or verification), multi-factor authentication, or login verification.
With MFA, access to your account requires two forms of ID:
- Something you know (such as a password).
- Something you have (such as a passcode, phone, or mobile app).
Set up your Microsoft 365 sign-in for multi-factor authentication
Authentication Methods
There are several options for authenticating with MFA, including a mobile device, desk phone, or security fob.
We encourage you to configure your office phone as a secondary MFA option. This ensures that you will have account access even when you don't have your mobile device.
If you want to review or update any of these methods, you can visit https://aka.ms/mfasetup
Authenticator App
The free Microsoft Authenticator app is our recommended way to authenticate. It is the fastest and easiest way to verify your identity. It is available for iOS and Android devices. This authentication method works by sending a push notification to your device to verify your login attempt. It also provides a rotating code you can type in if you cannot receive push notifications or don't have wireless service. If your phone supports biometrics, you can approve the login with your face or a fingerprint.
Do not approve Authenticator notifications that you did not request. If you receive a notification when you are not attempting to log in, deny the request and use the 'report as fraud' function within the app.
Other Authentication Apps
Other authenticator apps (Google Authenticator and Duo, for example) also provide MFA. However, these apps do not use push notifications as the Microsoft Authenticator app provides. You will only be able to use these apps by entering the code that they generate.
Phone Verification
When you select phone calls as your verification method, you will get a call to the number you provided. Follow the instructions to provide authentication.
Note: If you travel internationally, you should also register an authenticator app in addition to your phone number. Phone calls from Microsoft may not reach overseas cellular networks.
Text (SMS) Message
The text (SMS) message will contain a code to enter in the login window to provide authentication.
Note: If you travel internationally, you should also register an authenticator app in addition to your phone number. Phone calls from Microsoft may not reach overseas cellular networks.
Security Fob
If you do not have access to a mobile phone or desk phone, IT has a small number of security fobs that you can use instead. Security fobs are small (about the size of a key fob). Press the button on the fob to generate a number that can be typed into the authentication screen to confirm your login.

Note: Lost tokens must be purchased from IT for $11. Third party tokens are not supported.
Troubleshooting and Questions
An increasing number of campus partners are requiring FLCC to use MFA. SUNY security guidelines now require MFA, as does Brightspace LMS. Some of our insurance providers even require MFA. Our systems are under constant attack. Two of the most common attacks are password sprays, where attackers send thousands of logins using usernames and passwords harvested from the web, and phishing attacks, where attackers attempt to get your username and password. MFA can stop many of these attacks and is no longer considered an optional enhancement, but a required security measure.
If you would like a detailed analysis of how MFA protects logins, read Your Pa$$word Doesn't Matter. This article lays out Microsoft's research across explaining why passwords are insecure and how MFA results in protecting against all but the most targeted attacks.
Logins to some FLCC Enterprise Applications and Microsoft's OneDrive and Office will require you to sign in and use MFA at least every 14 days. Sign in frequency varies between services and is based on security and vendor requirements.
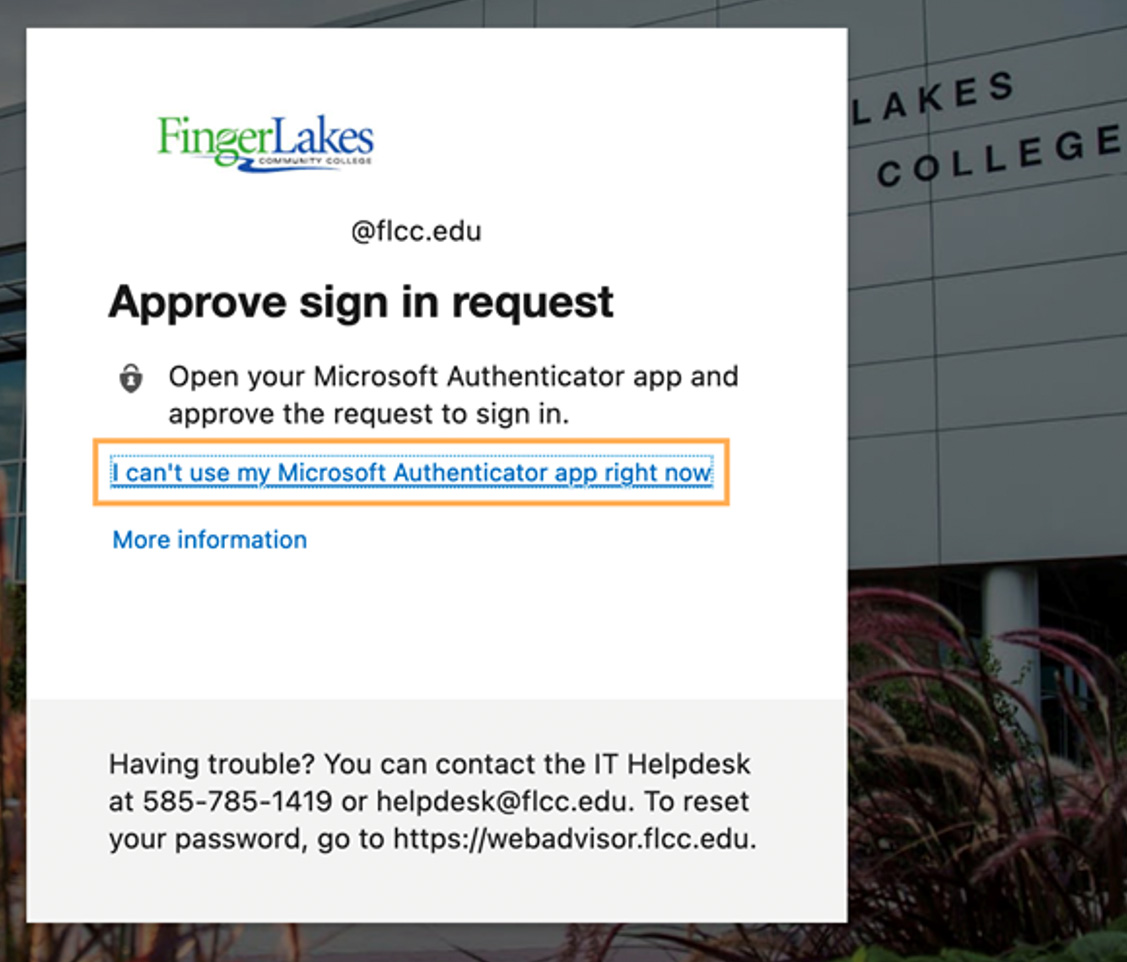
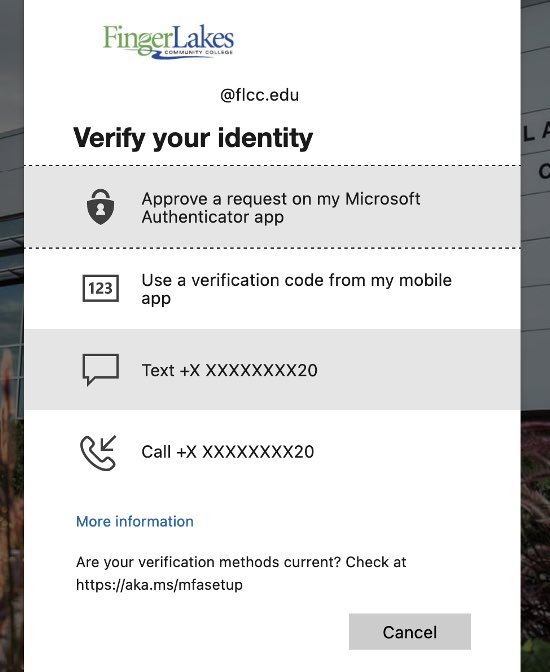
When prompted to sign in with the authenticator, click on "I can't use my Microsoft Authenticator app right now" button and select a new method.
If you lose your primary authentication device, you should notify the HelpDesk as soon as possible. The HelpDesk can help you register another method or reset an existing method.
Yes. Using a device for multi-factor login comes with the obligation to take reasonable precautions to protect it. This includes using a password or PIN to unlock the phone and updating your device to the latest operating system and Authenticator App.
Yes. Third-party apps such as 1Password, Duo, and Google Authenticator can be used to generate an OATH verification code. Users may have up to five OATH hardware tokens or authenticator apps such as the Microsoft Authenticator app configured for use at any time.
You should report all messages that you did not generate. This may be a sign of someone attempting unauthorized access to your account, and your password may be compromised. Deny the notification and then confirm that it's a fraudulent attempt. You should change your FLCC password after reporting the fraudulent login attempt.
Note: the authenticator app will warn you that reporting a fraudulent attempt may cause your account to be blocked or disabled, but this will only occur if you do not change your password in a timely manner.
The Microsoft Authenticator needs access to your camera to take a picture of the QR code (the weird barcode looking square) on your screen. It does not use camera access for anything else.
The Microsoft authenticator does not track you and it does not log location data. The only push notifications it will ever send you are approval requests for logins to FLCC systems. The Microsoft Authenticator does not give IT or Microsoft access to any data or information on your device.
If you would like to know more about the Microsoft Authenticator, please read the Authenticator FAQs.
You may not think you have access to any information worth protecting, but all our faculty and staff have access to secure information of one kind or another, from your W-2 (which an attacker could use to commit fraud and receive your tax return) to student health data, FERPA protected student data, or college financial data.
If your FLCC account is compromised, it can be used to trick other staff into responding to a phishing email. Your account can help an attacker to more easily access systems or compromise users that do have access to the data they are looking for, even if you don't have access yourself.
Contact Us
IT Helpdesk
Room 3300
(585) 785-1419
helpdesk@flcc.edu
flcc.edu/it
Helpdesk & Computer Lab Hours
Spring/Fall Semesters
Mon-Fri: 8:00 a.m. - 9:00 p.m.
Sat: 9:00 a.m. - 1:00 p.m.
Sun: Closed
Winter/Summer Sessions
Mon-Fri: 8:00 a.m. - 4:00 p.m.
Sat: Closed
Sun: Closed


